JWT
Stands for "JSON Web Token."
A JWT is an industry-standard token that shares security information between two parties. JWTs are compact and URL-safe, which allows web servers and clients to exchange them as part of an HTTPS request. The most common use for a JWT is for authenticating a user signed in to a website or web app, often through a single sign-on (SSO) service.
JWTs consist of three parts:
- The header includes information about the type of token and the algorithm used to generate the signature.
- The payload includes the list of claims made by the token. These claims typically include information about the token issuer, the website or web app using the token, and the user. They also include the time the token was issued and when it will expire (both using epoch time). In addition to these common values, a JWT may include arbitrary claims unique to the website or web app issuing the token.
- The signature verifies that the token hasn't been tampered with since being issued.
Websites and web apps often use JWTs as a stateless method of authenticating a user. They do not require that the server maintain a session in its memory or database, which reduces the overhead required for each user. Instead, the client and server trade the JWT back and forth with each HTTPS request, verifying the signature to ensure the token hasn't been altered. Once the JWT expires, the user must sign back in for a new one to be issued.
Creating a JWT
Both the header and the payload of a JWT consist of text written in JSON. The header and payload are each encoded separately using an algorithm called base64, turning several lines of text into a single string. The encoded header and payload strings are combined, separated by a '.' character.
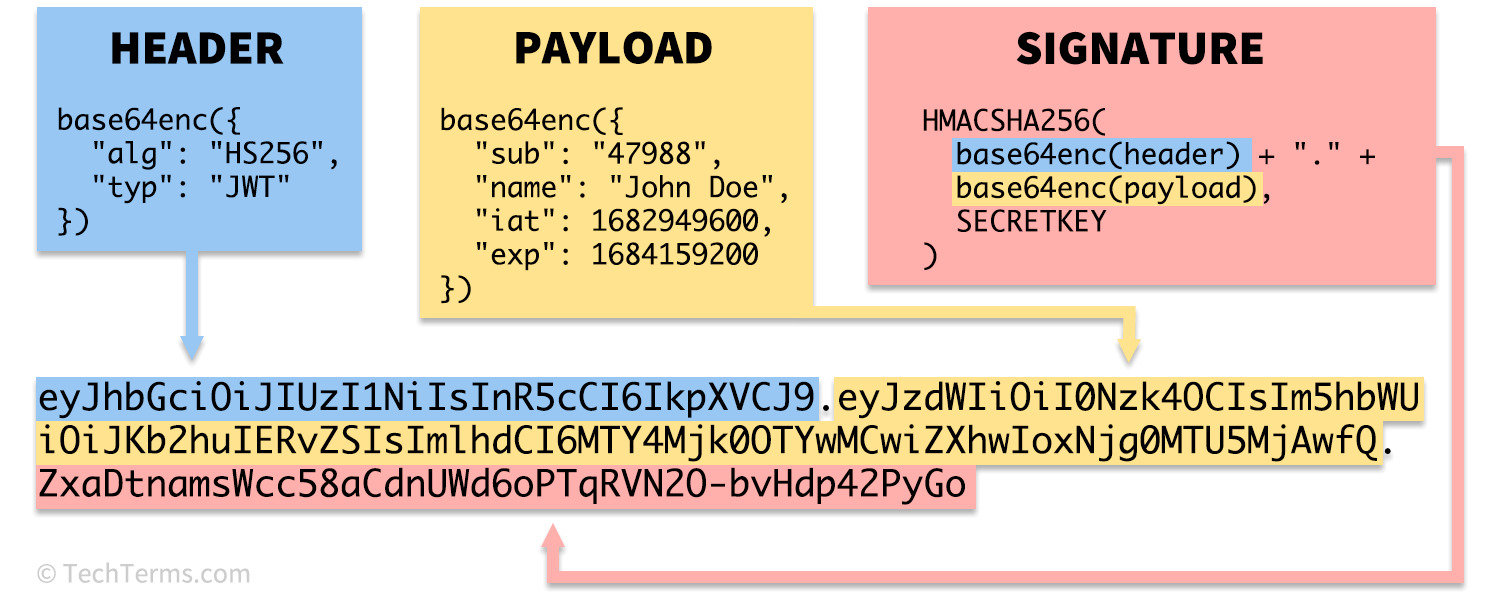
The combined string, containing the encoded header and payload, is encoded once again using a hash algorithm and a secret key to create the signature. The signature is then appended to the end of the header and payload, separated by another '.' character, to create the final JWT.
 Test Your Knowledge
Test Your Knowledge