Virus
A virus is a script or piece of malicious software that moves from one computer to another. It may spread through a social engineering attack that tricks a user into opening an infected file, or it may exploit software vulnerabilities to infect a computer without the user doing anything. A virus may delete or modify files on your computer or cause other performance problems as it consumes processing and memory resources. It may also expose your computer to unauthorized remote access, allowing hackers access to your personal files.
Infected email attachments are one common method of spreading a virus. Software downloaded from unofficial websites or pirate software networks may also contain viruses. Phishing emails and other social engineering attacks can also convince someone to install infected software or open infected files. Other viruses exploit bugs in operating systems and applications to spread without user intervention — for example, visiting a malicious website in a vulnerable browser.
Hackers have many reasons to write and spread viruses. Many do so for financial gain, either to steal valuable information (like bank account numbers and passwords) or to extort victims using ransomware. Some spread viruses to add computers to a botnet for participating in DDoS attacks. State-sponsored hackers create targeted viruses for militaries and intelligence organizations that can steal state secrets and damage infrastructure as part of a cyber warfare attack. Some hackers create a virus to create a name for themselves or to prove their worth before joining a hacking group, while some do so simply to cause harm by destroying data and crashing servers.
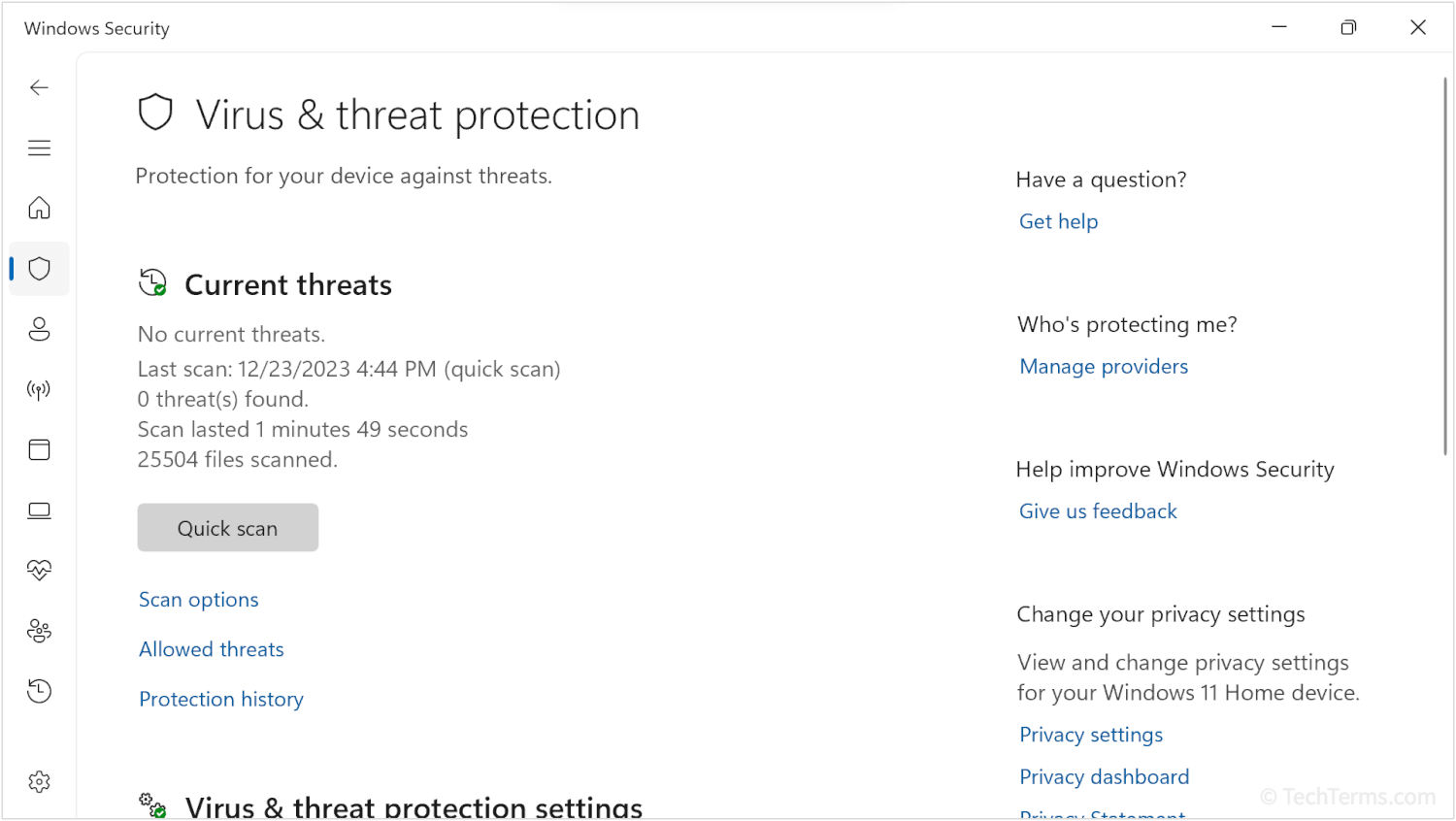
A virus infection may be difficult to remove, so it's best to prevent one before it happens. Antivirus utilities check all incoming files for viruses and run recurring full-disk scans to examine existing files. Keeping antivirus software and virus definitions up-to-date ensures that it knows about new viruses as they're discovered. Finally, it's wise to avoid files and programs from suspicious or unknown sources (particularly email attachments) and install updates to your operating system and applications that patch vulnerabilities.
 Test Your Knowledge
Test Your Knowledge