Trojan Horse
A Trojan Horse is a software program that masquerades as legitimate software but secretly contains a virus or other types of malware. When you run a Trojan horse, its hidden malware is installed and infects your computer. Trojan horses are one of the most common ways for malware to spread, taking advantage of vulnerabilities in human behavior instead of a computer's software.
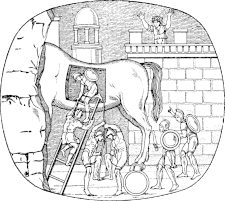
The name comes from the ancient myth of the Trojan Horse. Greek soldiers, unable to penetrate the defenses of the city of Troy during a years-long war, presented the city with a peace offering of a large wooden horse. The Trojans accepted the gift and brought it inside the city walls. Later that night, after the city was asleep, several Greek soldiers emerged from the horse to open the gates and allow the rest of their army inside to conquer the city. Like the ancient wooden horse, a Trojan horse pretends to be something useful — a piece of software you want to run like a game, system utility, or even an antivirus program. However, once you run the program, it turns out to be something different, installing unwanted malware and viruses.
Thankfully, there are defenses against Trojan horses. Antivirus software that monitors downloaded files can usually detect Trojan horses, and intercept the malware they contain if you do open them, as long as the virus definitions are kept up-to-date. Even if you have antivirus software installed, the best way to defend against them is to be mindful of what files you open. Be careful, and do not open software or files from unknown or untrusted sources.
 Test Your Knowledge
Test Your Knowledge