Soft Token
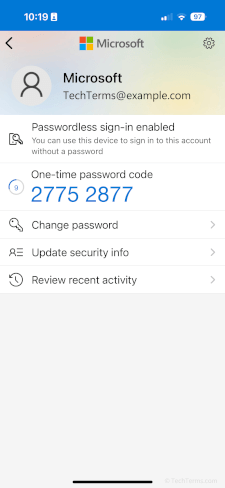
A soft token, or software token, is a piece of software that authenticates a user as part of a multi-factor authentication system. The most common form of soft token is an authenticator app, which can generate one-time-use passwords that add a level of security beyond a regular username and password. They are similar to hard tokens but exist as software on a device instead of a piece of dedicated hardware.
Soft tokens allow you to use a smartphone (or other device) as a part of a multi-factor authentication process. First, the authentication server generates a secret key for you to enter into your authenticator app. Once the secret key is in place, the authenticator app can generate one-time-use passwords, which are typically valid for 30 to 60 seconds each. The authenticator app generates passwords using the same algorithm as the authentication server; as long as the clocks on the server and the authenticator app are in sync, the passwords will match and authenticate the user.
While both hard and soft tokens add an extra layer of security to the authentication process, soft tokens do so with a little more convenience to the user. Hard tokens are small devices you need to carry with you and are useless if you forget them, but soft tokens live on the smartphone you're already likely carrying. An authenticator app may also utilize the smartphone's biometric security features like fingerprint scans or facial recognition, adding another level of protection. Finally, if a smartphone with your soft token is lost or stolen, your administrator can revoke the existing key and replace it with a new one that you can add to a new device instead of waiting for a replacement hard token.
 Test Your Knowledge
Test Your Knowledge