PCAP
Stands for "Packet Capture."
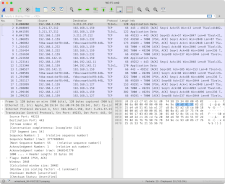
PCAP is an API for capturing computer network data packets. It records and saves traffic data logs in a standardized format, readable by any traffic monitoring and analysis tool. Network administrators use packet-capturing tools to obtain detailed information on data packets traveling over a network without disrupting that traffic.
Packet capture tools, also called packet analyzers or packet sniffers, use the PCAP API to intercept and log data packets that travel over a computer network. Network administrators may choose to capture the entire data packet or just the information contained in the packet's header. After capturing the data, the packet capture software can export the information to a log file and display it in a human-readable format. This information may include the time that the data packet was intercepted, its source and destination IP addresses, the data protocol used, and the packet's size. Some tools may also capture the data packet's payload itself, but can only analyze its contents if that data is not encrypted.
Network administrators use packet capture tools to monitor unusual activity and identify the sources of network problems. For example, captured packets can help detect a computer on the network with a malware infection by revealing a large number of data packets from that computer's IP address to a single remote server.
NOTE: Packet capture tools save logs using the .PCAP or .CAP file extensions. Any software that supports the PCAP API for packet capture can open and display these files.
 Test Your Knowledge
Test Your Knowledge